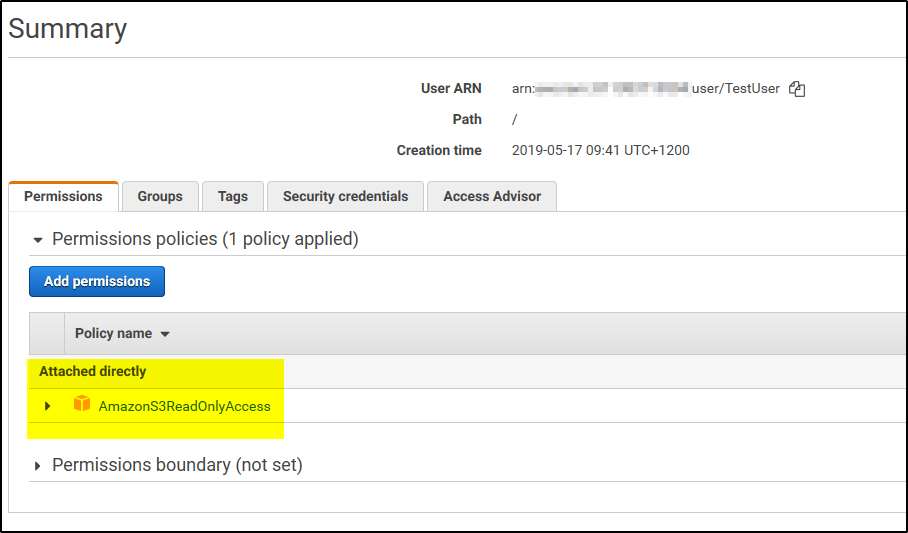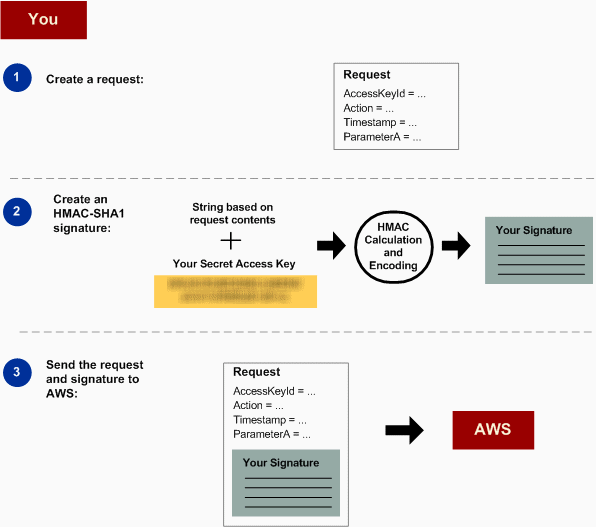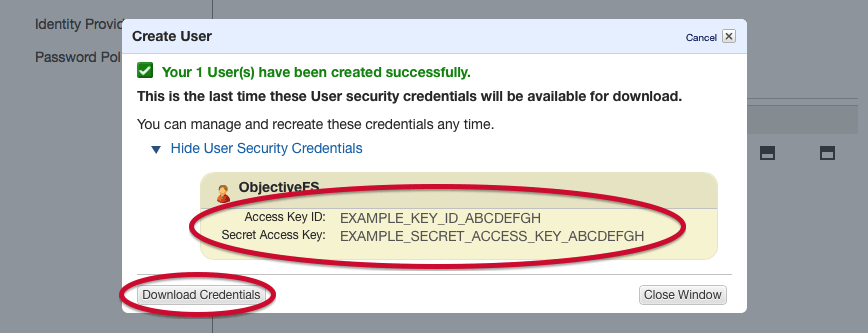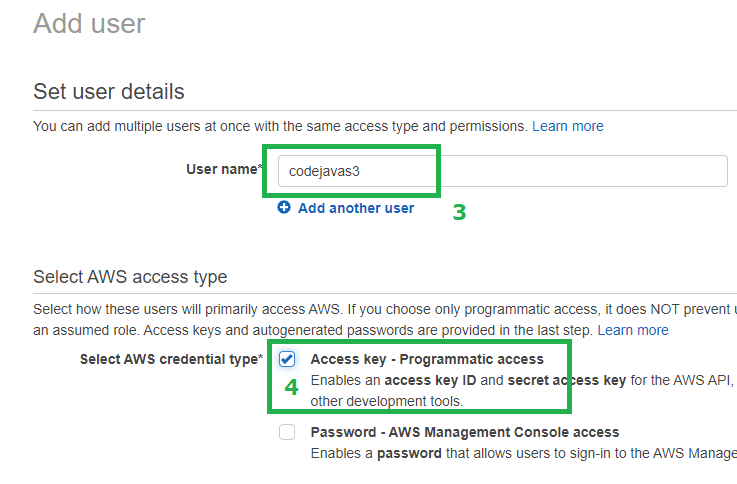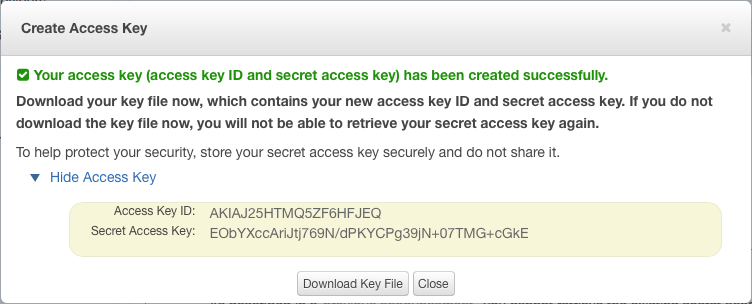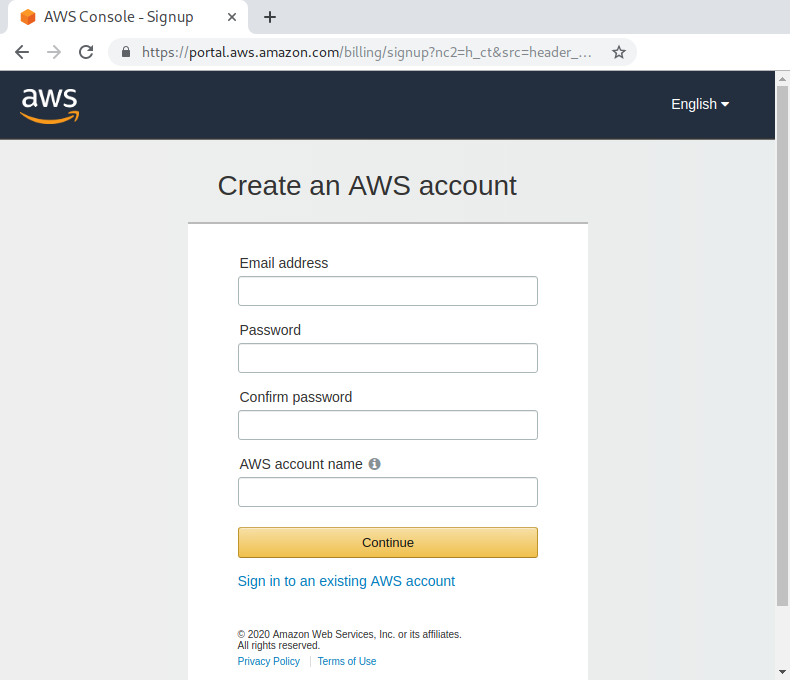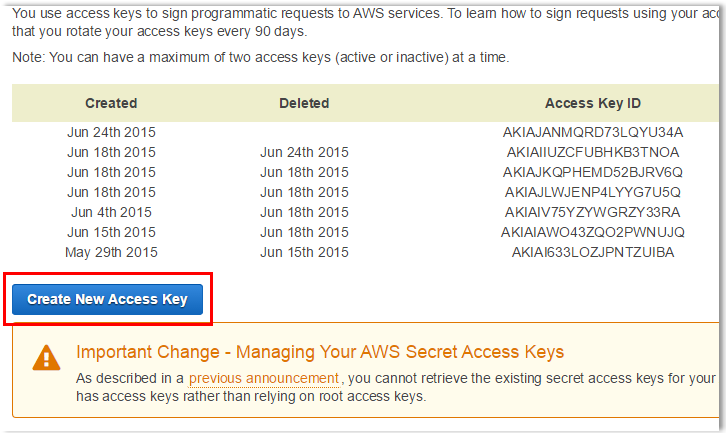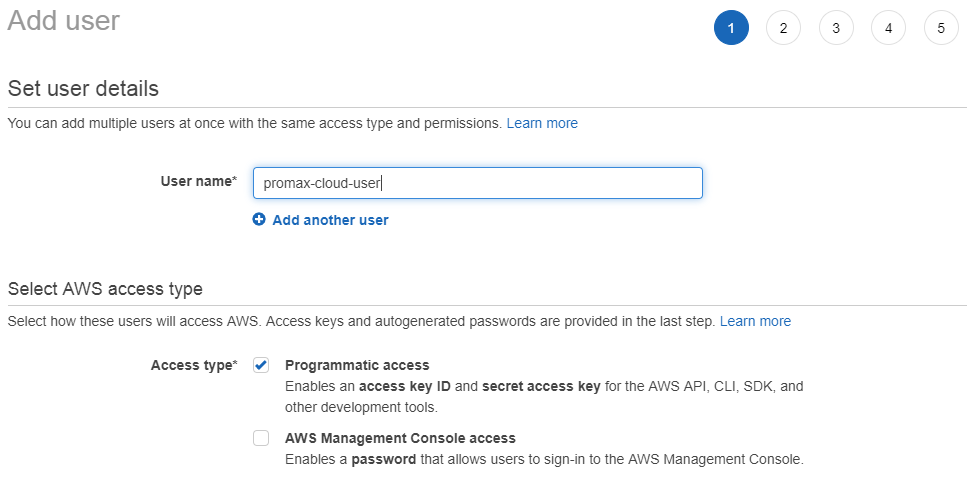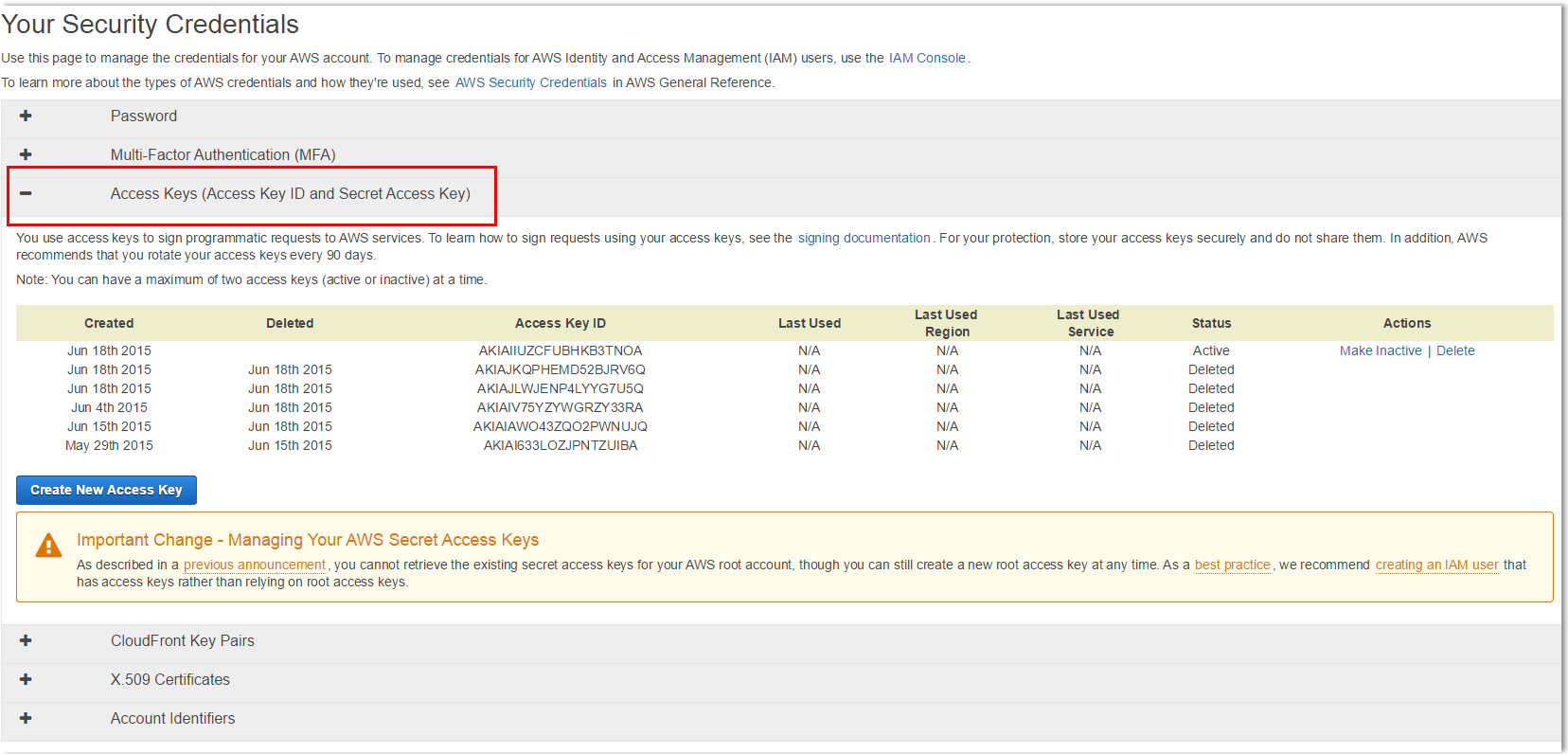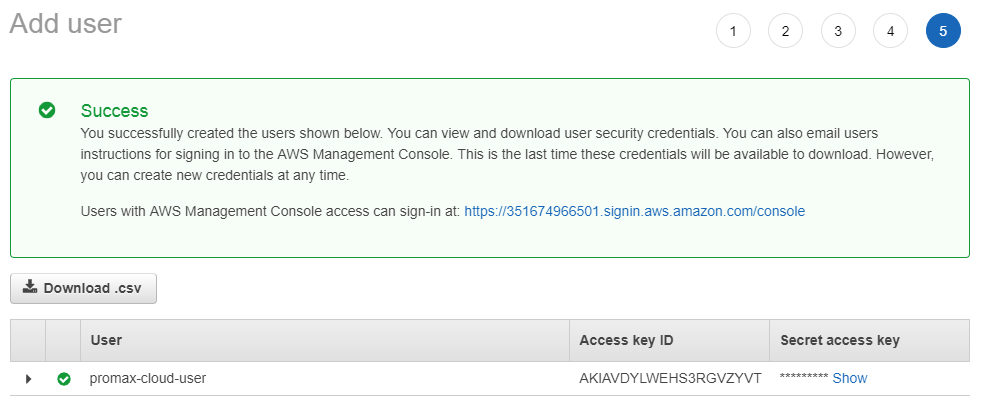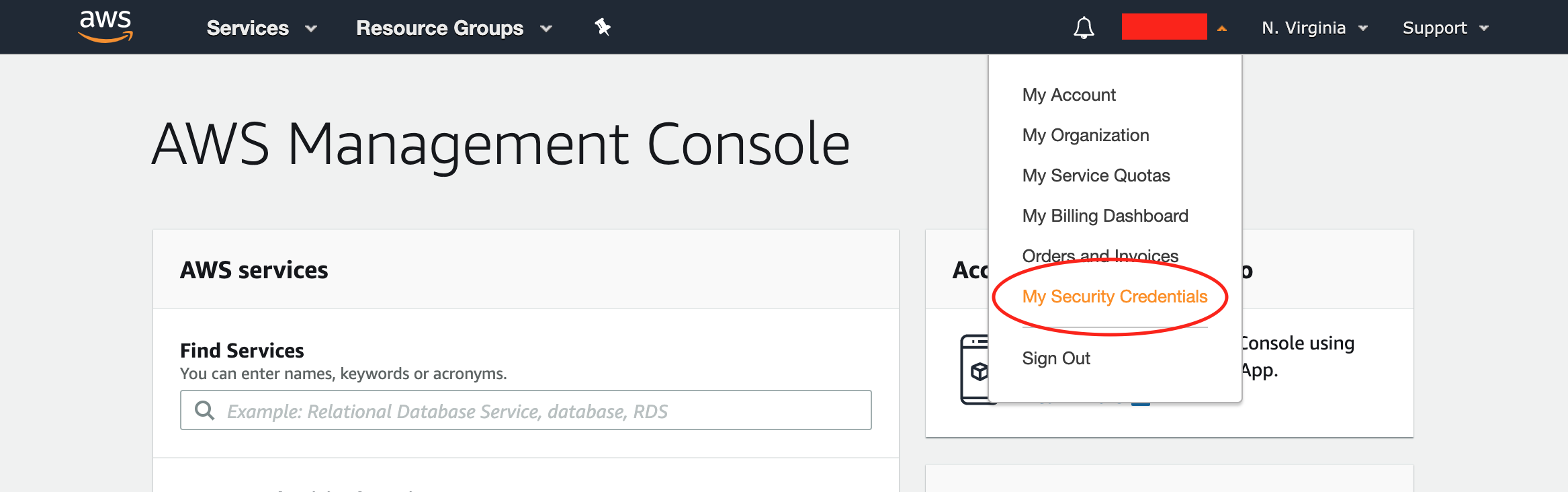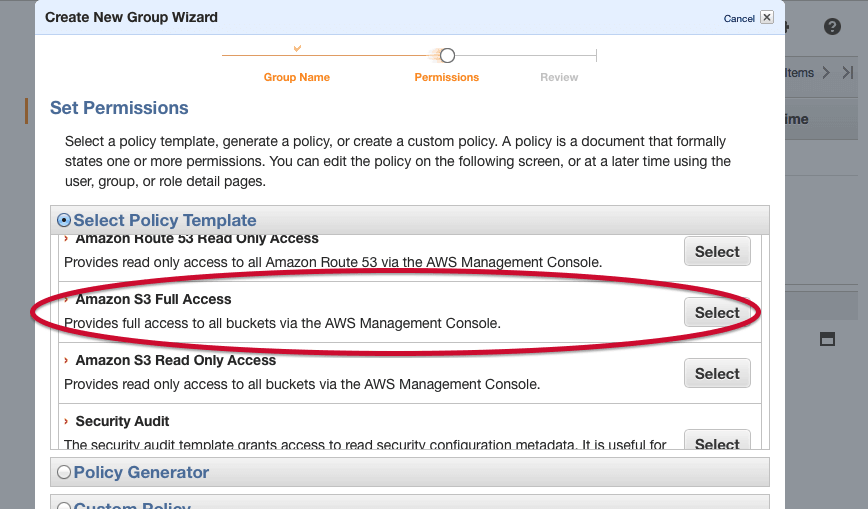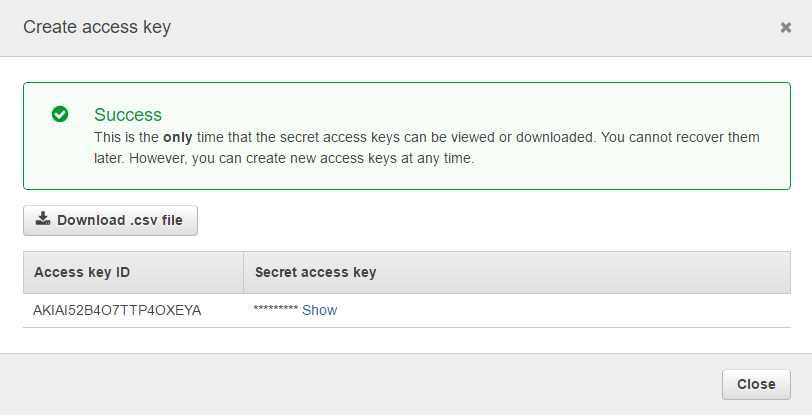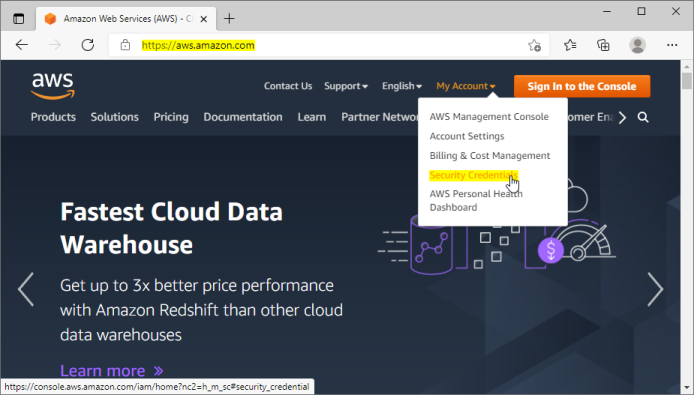
Access Key Id and Secret Access Key. How to retrieve your AWS Access Keys and use them to access Amazon S3.
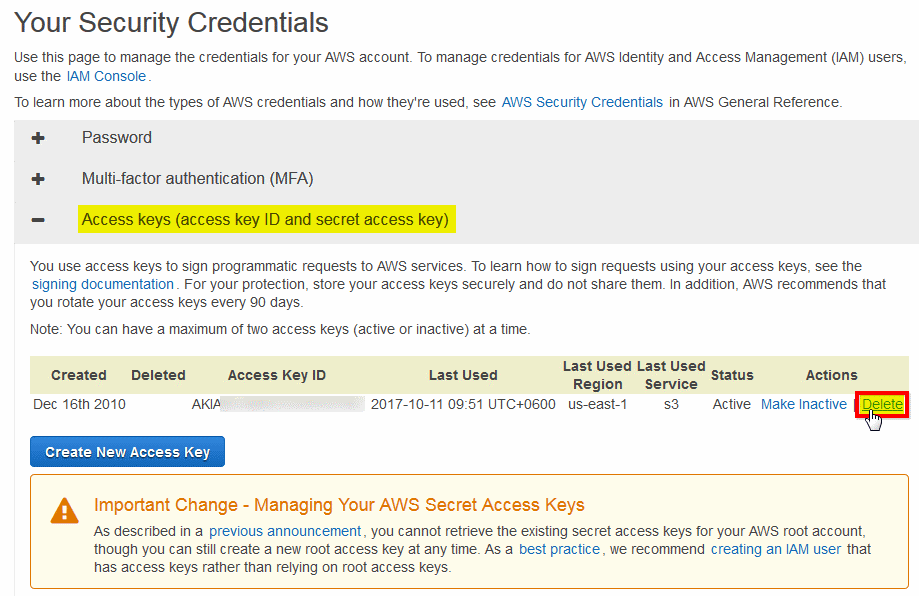
AWS Access Keys - Access Key Id and Secret Access Key. Where to obtain Access Keys and how to use them to connect Amazon S3.
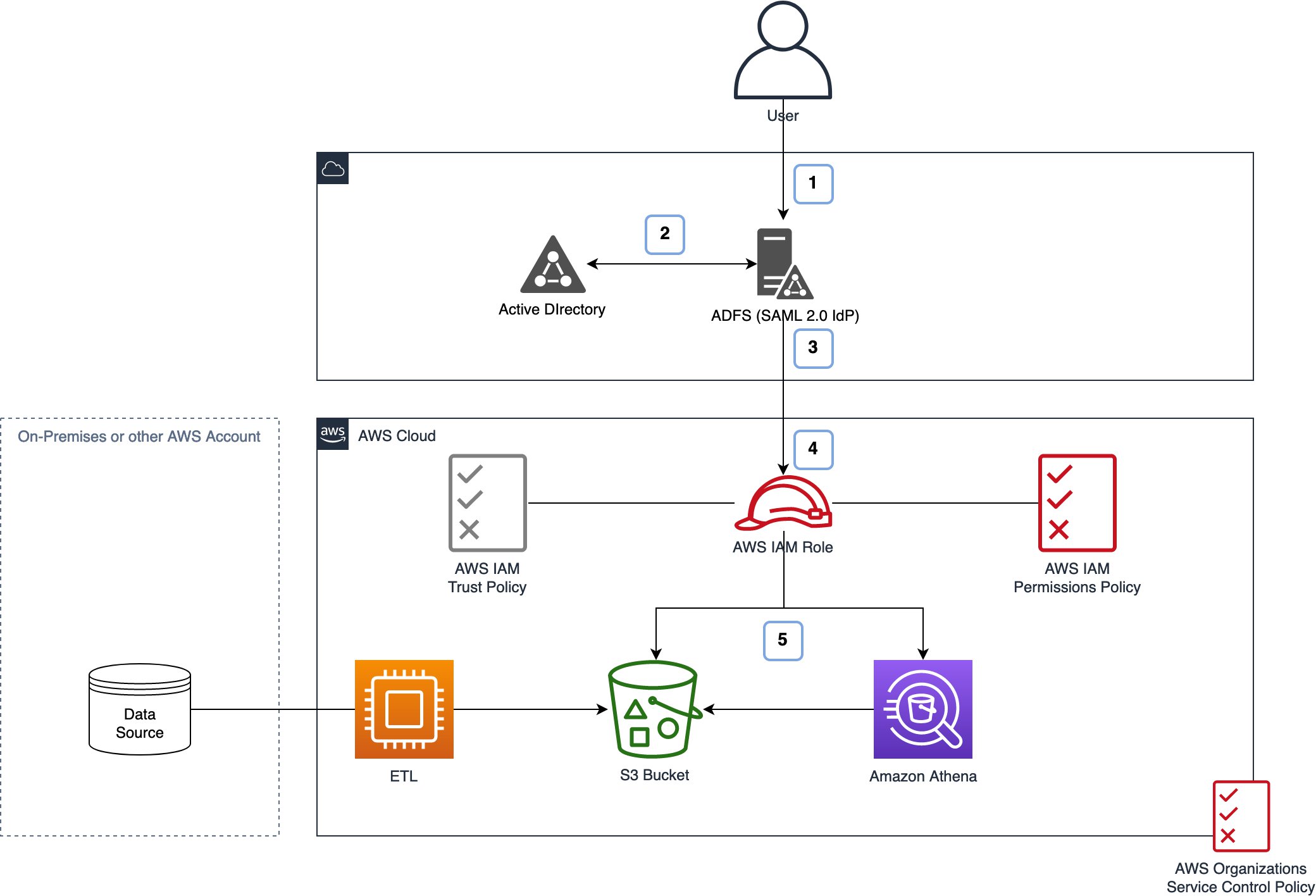
How to scale your authorization needs by using attribute-based access control with S3 | AWS Security Blog

How to Use Bucket Policies and Apply Defense-in-Depth to Help Secure Your Amazon S3 Data | AWS Security Blog
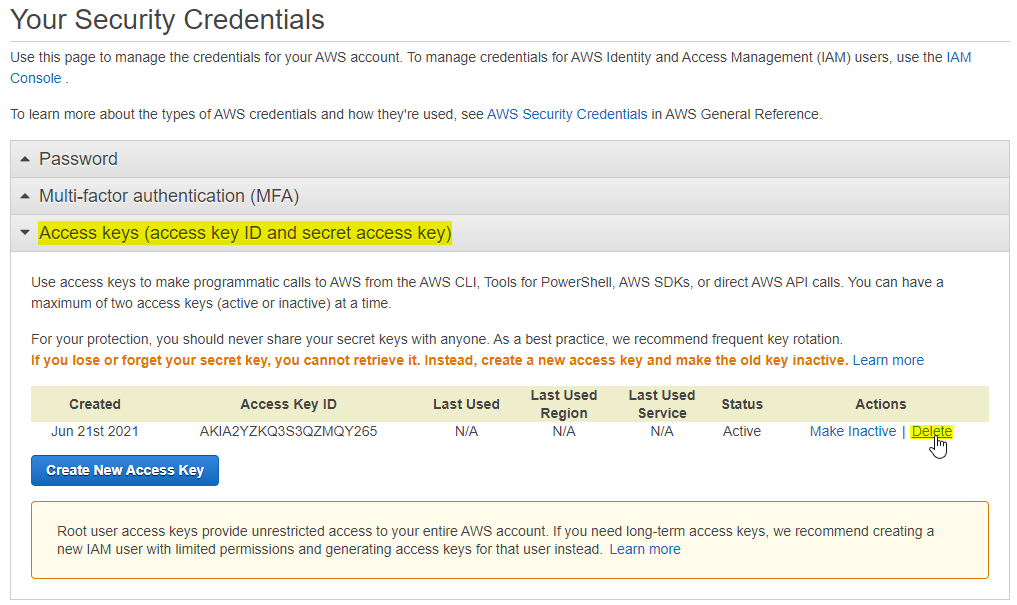
Access Key Id and Secret Access Key. How to retrieve your AWS Access Keys and use them to access Amazon S3.